
You can refer to it as the singularity. One day in the near future (or far), maybe a couple years and maybe a decade from now, you will hear a shocking message flashing all over the internet: "Bitcoin has been hacked!" or "Elliptic curves have been cracked!"
Now, you may wonder what is the Elliptic curve? Elliptic Curve Cryptography or better known as its shorter form, ECC, is literally the basic foundation of the Bitcoin network and what this entire network is built on. Now just think about the day someone actually discovered a hole in its code. Only a simple vulnerable point is needed in the entirety of this code in order for Bitcoin to be destroyed and for all the exchanges to be taken down.
Bitcoin’s Security

Brian Armstrong, the co-founder of Coinbase (the largest crypto exchange in the United States) and the person who is currently running it, has talked about this particular issue in one of his interviews at the company's headquarters in San Francisco. He did admit that there wasn't a way for him to actually prove that there wouldn't be some mathematical ways to compromise Bitcoin keys though the chance of such an event actually happening is quite low. "Bitcoin has been around for over 10 years and has been using the same code for the entirety of its existence. After all these years, there are tons of people who have looked at this code and have gotten somewhat familiar with it”, as he stated in his interview. He referred to Bitcoin as a bounty worth 100 billion dollars.
Bitcoin, a Huge Bounty
Bitcoin along with some of the lesser cryptocurrencies that are competing with the most famous crypto right now are a pile of assets with the tempting worth of $280 billion that are ready to be cracked by a lucky person. This is quite the goal for the bad guys. From the very first day Bitcoin was created, when it was only a couple of days old, till now that it has become a giant in the world of cryptocurrencies, hacks, cracks, phishes, hijacks, vishes, and social engineering have been threatening it. Hopefully, none of the attempts were successful so far. The most successful assaults on Bitcoin have been only around the edges and even the big heist at Mt. Gox was not able to kill the cryptocurrency but this does not, by any means, mean that it will always stay like this.
What would happen if there was a vulnerability in Bitcoin?

Let's imagine the day when a thief or a group of them discovers a fundamental vulnerability in the code. The vulnerability might be in the global network of computer nodes which track ownership of Bitcoin or it may be in Bitcoin's encryption method and the way it works. It might also be in some part of the cryptocurrency that not a lot of people are thinking about and therefore not expecting it. What do you think would happen? Surely Bitcoin has some kind of emergency alarm programmed for such a scenario.
There are two answers available for the question above and both are still a theory.
1. Defensive State
The first theory / answer is that in case of an attack, Bitcoin's network acts up just the way a country would if a nuke was launched towards them. They would immediately go into a blast shelter in order to reduce the casualties to a minimum. So, our guess is Bitcoin's node moves to a different protocol as soon as a weak spot is discovered on its 11 year old encryption system to prevent any coins from being stolen. An alternative to this type of defence is that Bitcoin actually goes back to an earlier version of the blockchain from before any theft had happened. This is the exact method Ethereum used to undo an attack on its network before.
2. End of Cryptocurrency
Now comes theory number 2. The second answer, however, is not as reassuring as the first one. There is a lot more than Bitcoin at stake in the case of such an event happening. “A core math problem? It’s the collapse of the whole Internet we are talking about here.” As stated by Philip Martin who is head of security for Coinbase. The encryption protects trillions of dollars moving via transactions through the electronic networks.
Bad Implementation
Once, there was a time when Sony actually used the same encryption – Elliptic Curve Cryptography – in order to protect its infamous console, PlayStation. A game had to provide a digital signature to be able to run. The signature was created from Sony’s secret key, which is exactly the same type of key that Bitcoin uses to protect your crypto assets. The signature pattern takes one randomly selected number for validation.
The problem is that Sony was not successful with this method since they recycled the same number. What this means is that someone with at least 2 legit games could easily pirate other games with some knowledge of algebra from high school.
Now, you may think all of these flaws were found a long time ago so they must have been fixed by now. Right? Well, the answer is no. Just recently, there was a flaw reported in a Microsoft browser in which a mistake occurred when delivering digital signatures that are able to verify the legitimacy of a website. ECC calls for the need of using a starting point but the problem is that it is possible for it to slip in a different point due to a certain flaw. With that said, a malicious website could easily have forged a digital signature with just the right substitute. This means someone could easily use the same encryption Bitcoin’s network is using to steal your password for the bank account.
Now, this was about Microsoft and hopefully they fixed the issue immediately before disasters started to occur. You might be thinking so what does this have to do with Bitcoin. Well, if such a problem once existed, other problems could also exist which makes Bitcoin’s encryption vulnerable. It’s good to know that some of the people who own bitcoins in their wallets have also made the same mistake as Sony and Microsoft. Due to these mistakes, a lot of Russian hackers have programmed bots that are able to take coins from vulnerable addresses automatically. Hopefully, Bitcoin’s main network is still safe and only people who make this mistake allow the hackers to enter their wallets which is really not that big of a problem if you hire experts to manage your bitcoin wallet.
Social Engineering

Until now, we have discussed that Bitcoin is really hard to hack and no one has ever been able to even come close to it but there is one more thing we have to consider. Hacking the system doesn’t always involve cool command lines in green screens from the Matrix. That means hacking Bitcoin does not require the hacker to be a master in algebra or mathematical problems. A person with good acting abilities and social skills might do it as well. These people are masters of deception and can manipulate people who are not careful into opening up the security doors for them.
Mathematical Hacks
Encryption methods that are being used commonly today, seem to be secure and are mostly so, since they have been under hours of study from experts. Still, someone may find a tunnel into the system and extract whatever they need.
The way encryption works is by scrambling numbers. One of the methods to do this – in the RSA scheme which is still widely utilized by many people in order to protect sensitive data from being leaked – uses exponentiation and modular arithmetic.
51% Attacks
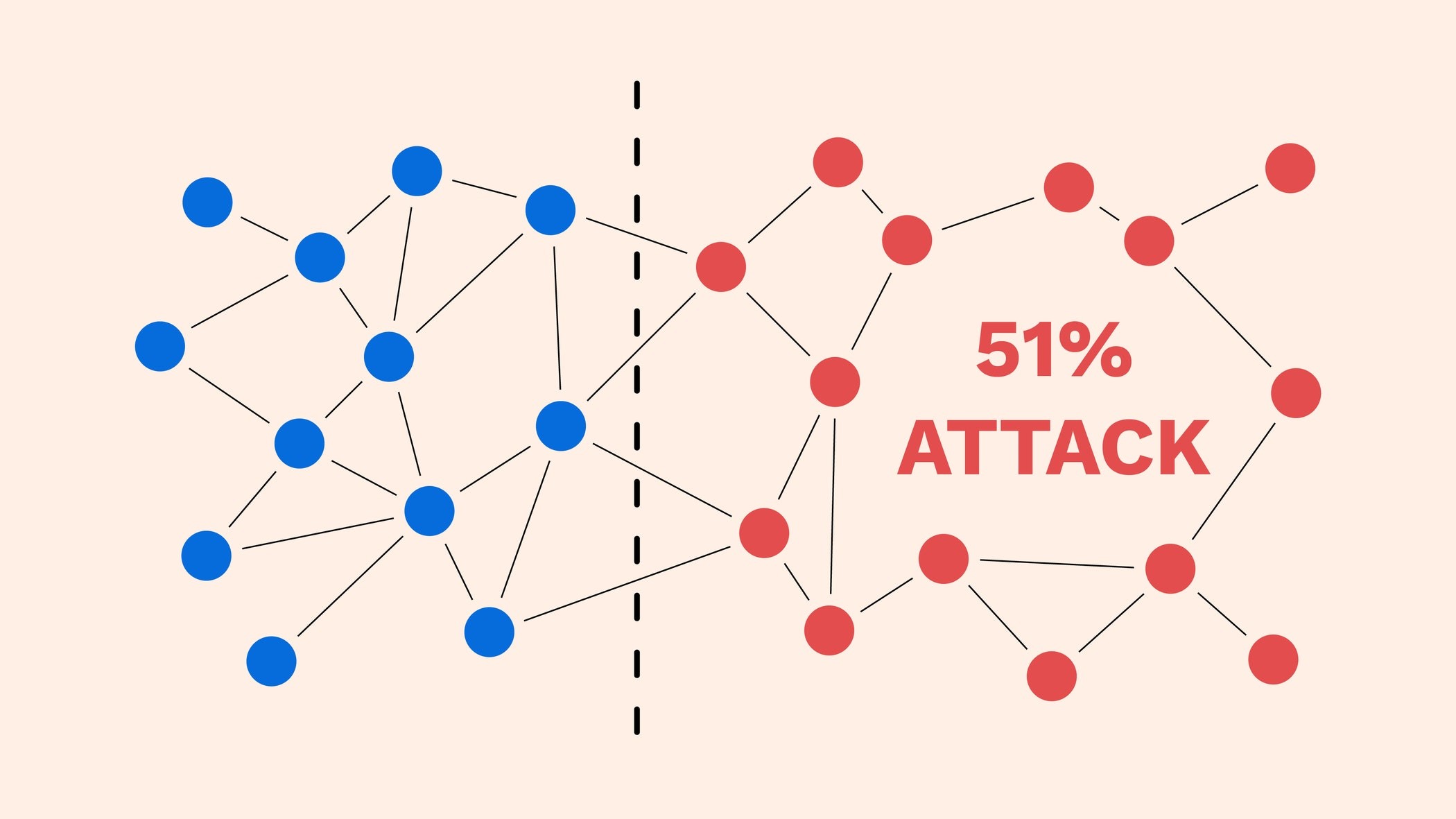
A 51% attack is when a miner or a group of them somehow gets control of more than 50 percent of a cryptocurrency’s blockchain. These attacks are one of the biggest threats for those who buy and trade cryptocurrencies. Luckily, a 51% attack on Bitcoin is not all that common due to the logistics and the cost of the hardware needed to do one of such attacks. Keep in mind though that in case a 51% attack occurs on Bitcoin’s blockchain, it might have huge and long-lasting effects on the cryptocurrency’s market and its investors.
Exchanges and Wallets
Bitcoins are stored in wallets and can be traded via currency exchanges. Each Bitcoin user is given a unique private key as well as a public one. The private key lets you gain access to your crypto assets in the wallet and obviously, must remain private. Do keep in mind that in case your private key is compromised, then hackers can and will infiltrate your wallet and steal the BTC stored in it. Also, if you own a hardware wallet and some malicious person gets hold of it, you might lose a lot of bitcoins.
It is also possible that the hacker attacks the exchange instead of attacking Bitcoin’s network directly. Most of the exchanges offer security measures such as two step verification but there is still a small chance of a bug or glitch in the system which acts as a back door to the system for the hacker. Besides that, you should protect your credentials at all costs. Compromising your password is a really easy and common way for hackers. Make sure you are always aware of their tricks and deception.
The Final Takeaway
Ever since the creation of cryptocurrencies and especially Bitcoin, thousands and even millions of coins have been lost in hacks, scams, and Ponzi schemes. Unfortunately, these have been here from the beginning and there is no doubt they won’t stop here either. But these are not nearly as disastrous as the big knock over in which the whole network of Bitcoin gets hacked. Although such a catastrophe is probably not going to happen and the probability is really low, still, it is not zero and anything with a probability of more than zero can occur.
Bitcoin Network
Bitcoin’s Security
Brian Armstrong
Vulnerability in Bitcoin
Social Engineering
Graphic Photo World
Frontend Free Code
Code Free Tutorial
CSS Free Code
PHP Free Code



 Home
Home How to use
How to use Sitemap
Sitemap About Us
About Us Suggested
Suggested Privacy Policy
Privacy Policy